
How to prevent fraud

Outsmart tax scams and keep your finances safe

How to report a scam

How to spot a credit repair scam

How to spot an online scam

Money muling 101: Learn how money mule scams work

How to avoid student loan scams

What is financial fraud?

Your go-to checklist for managing elderly parent's finances

Don’t let an uptick in scams ruin your holidays

7 ways to improve checking account security

5 tips for seniors to stay a step ahead of schemers

Is online banking safe?

How-to guide: What to do if your identity is stolen

7 ways to teach your children to be smart about online scams

How to avoid falling for scams targeting digital payments

Student loan scams and other common student scams to be aware of

Banking basics: Avoiding fraud and scams

What you need to know about identity theft

Protect yourself from financial exploitation

8 tips and tricks for creating and remembering your PIN

How to keep your assets safe

Essential tips for preventing check fraud

Lessons learned from experiencing a scam
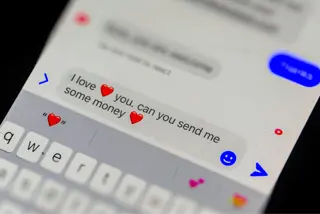
What to know about romance scams

Kick off the new year with a cybersecurity boot camp

8 of the newest scams targeting your money


